Supply-chain compromise of LiteLLM
Supply-chain compromise of LiteLLM
An attacker hijacked maintainer credentials via poisoned CI dependency, published legit-package backdoors with auto-executing infostealer (.pth) exfiltrating cloud, SSH, K8s, and crypto secrets, plus persistence/C2.
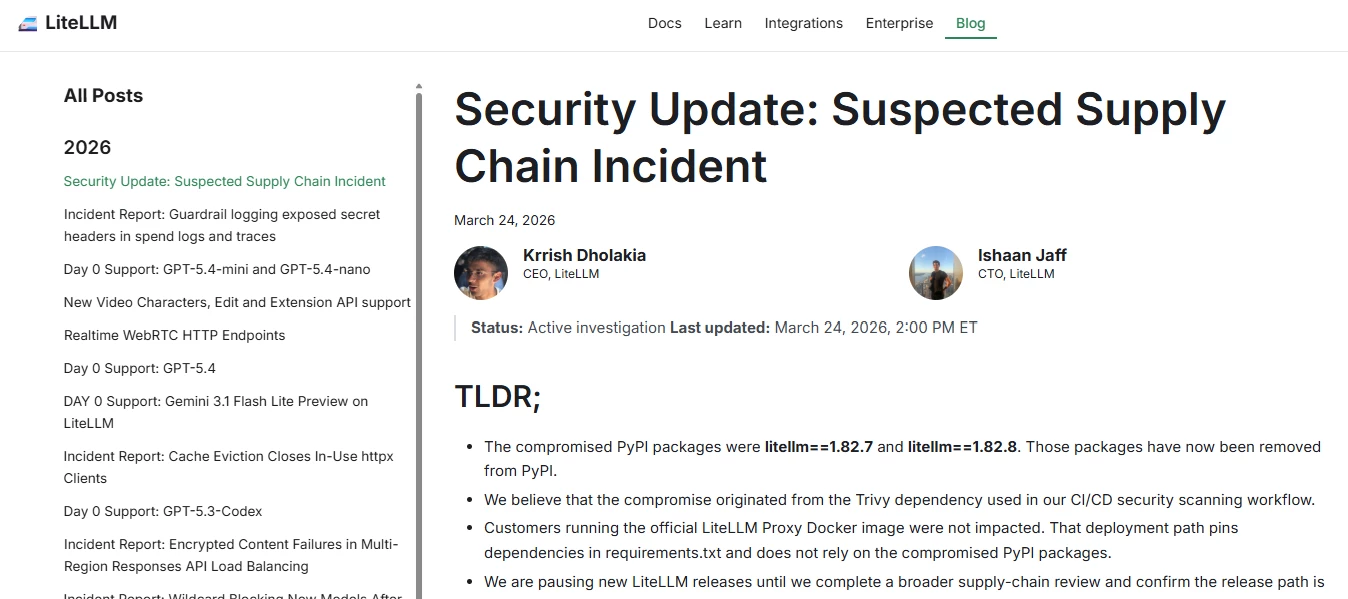
According to LiteLLM only PyPI versions 1.82.7/1.82.8 had malicious packages, injected via compromised CI (Trivy). Official Docker image (pinned deps) unaffected; releases paused during audit. Malware enabled full credential exfiltration and persistence.
LiteLLM’s guidance:
-
Uninstall affected versions (1.82.7/1.82.8) and reinstall a safe version (≤1.82.6)
-
Rotate all credentials (cloud, API keys, SSH, etc.) immediately
-
Audit systems/CI for compromise & persistence (hosts, containers, clusters)
-
Pause/secure release pipelines and review supply chain (CI/CD, dependencies)
-
Prefer pinned/isolated deployments (e.g., Docker with locked deps)